The MNC Blog
Our official blog with news, technology advice, and business culture.
How to Ensure Compliance to Data Destruction Laws in 2025
In 2025, data privacy and protection will continue to be one of the most important aspects of digital compliance. As organizations gather vast amounts of sensitive data, it becomes more important to safeguard that data. The laws governing destruction of data are a vital element of this obligation protecting the privacy of individuals and ensure that businesses adhere to regulations for the disposal of data. This blog will provide you with how you can stay in compliance with the laws governing data destruction in 2025. We will discuss all important laws, best practices, and essential information for maintaining the security of your data.
Top 5 Benefits of Using Certified Refurbished Servers
With the ever-changing technology landscape, companies are finding ways to improve their IT infrastructure while remaining within their budgets. Servers, as the core of every IT infrastructure, typically come with a high cost, which makes it challenging for smaller and medium-sized companies (SMEs) to purchase modern technology. That’s where certified used servers can be used, offering an ideal alternative for companies looking to purchase top-quality equipment with minimum expenses.

Signs Your Business Needs an ITAD Strategy
In the digital era, businesses are constantly upgrading and replacing IT equipment to keep up with the latest technologies. As companies upgrade their systems, old hardware—whether it’s laptops, servers, or mobile devices—can pile up. Improper disposal of this equipment can expose businesses to data breaches, regulatory fines, and environmental disturbance. That’s why an IT Asset Disposition (ITAD) strategy is important.

The Business Case for ITAD-Specific ERP: Why Generic Systems Don’t Work
In the dynamic world of IT asset disposition (ITAD), businesses are under constant pressure to keep updated with rapid changes. From improving efficiency to protecting sensitive data and staying compliant with ever-tightening regulations, the challenges can seem overwhelming. So, how can companies stay ahead and manage it all? The key is adopting solutions built specifically for the specific needs of ITAD.

Cybersecurity in the ITAD Lifecycle: Why Data Destruction Alone Isn’t Enough
In today’s digital age, protecting sensitive information is more critical than ever. With cyber threats on the rise and the growing complexity of IT systems, organizations must adopt comprehensive data security strategies to ensure that their information remains secure, particularly throughout the lifecycle of their IT assets. This includes everything from procurement to disposal, particularly the IT Asset Disposition (ITAD) process, where proper data destruction is a key aspect. But, while data destruction is undeniably important, it’s not the whole story.

Meeting NIST, HIPAA, and ISO Standards: Cybersecurity Best Practices in IT Asset Disposition (ITAD)
In today’s rapidly evolving digital landscape, ensuring the security of sensitive data during IT asset disposition (ITAD) is more critical than ever. With the increasing number of cyber threats, businesses must adhere to stringent cybersecurity standards and regulations to protect sensitive information. Among the most important of these are the NIST (National Institute of Standards and Technology), HIPAA (Health Insurance Portability and Accountability Act), and ISO (International Organization for Standardization) standards. But what do these standards mean for ITAD, and how can organizations meet these requirements while ensuring data security? Let’s delve deeper to gain a better understanding.
What is IT Asset Disposition (ITAD) & Why It’s Essential for Businesses
In an era where businesses generate terabytes of data daily and upgrade hardware every few years, the end-of-life management of IT assets has never been more critical. Consider this: the global IT Asset Disposition (ITAD) market was valued at $17.4 billion in 2024 and is projected to grow at a 7.7% compound annual growth rate (CAGR) through the decade, driven by escalating concerns over data security and electronic waste (e-waste). Yet, many organizations still treat outdated servers, laptops, and storage devices as mere trash, risking data breaches, regulatory fines, and environmental harm.
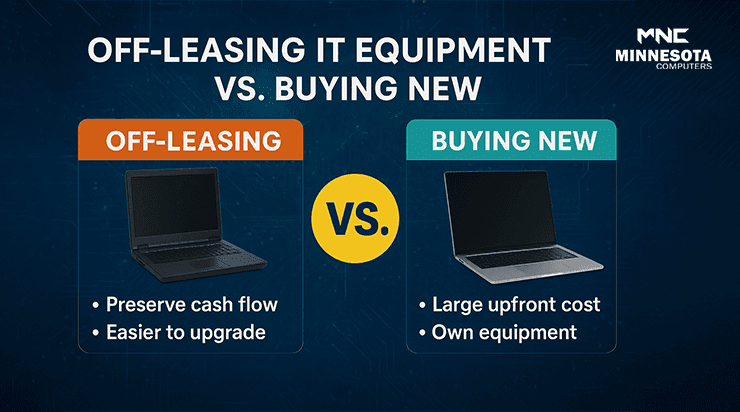
Benefits of Off-Leasing IT Equipment vs. Buying New
The cost of IT hardware is rising, as the global market is predicted to reach $174 billion by 2027. Businesses are under increasing pressure to keep up without depleting budgets. Off-leasing IT is an alternative that is cost-effective, offering quality, refurbished equipment at just a fraction of the price of brand new. From servers to laptops, off-lease equipment can save cash, improve flexibility, and suitable for businesses of any size.